EIGRP STUB
First a heads up - it's a bit complicated because there are just too many details... Subjective impression!
The command is rather straight forward:
Cisqueros_1(config-router)#eigrp stub connected [connected | summary | static | receive-only | redistributed]
When the EIGRP process is configured as STUB on a router using the "stub connected" command:
Cisqueros_1(config-router)#eigrp stub connected
There are a few things that we need to remember:
- That router will no longer see Connected routes, ONLY the Summary (if configured), and also Static and Redistributed routes (because the STUB doesn't affect the Router where it's configured)
- The EIGRP Neighbor(s) will NOT see the Summary, Static or Redistributed Routes, ONLY the specific routes BECAUSE ONLY Connected Routes are advertised
If however we use the "stub summary" command to configure the STUB:
Cisqueros_1(config-router)#eigrp stub stub summary
- The router will keep the same EIGRP routes in the routing table
- The EIGRP Neighbor(s) will ONLY see the Summary
Now with the "stub static" or "stub redistributed":
Cisqueros_1(config-router)#eigrp stub stub [static | redistributed]
This router keeps behaving exactly the same, while the EIGRP Neigbors ONLY receive the Static OR Redistributed routes
With the "stub receive-only":
Cisqueros_1(config-router)#eigrp stub receive-only
This router keeps behaving exactly the same, while the EIGRP Neigbors stop receiving ANY routes from the Router
And finally the "eigrp stub" command can be configured without any attributes, so just:
Cisqueros_1(config-router)#eigrp stub
in which case the EIGRP neighbors ONLY receive the Summary Route
EIGRP Authentication and some EIGRP "tuning" options
EIGRP Authentication
Like in OSPF - the configuration is done in the Interface Configuration mode. Unlike OSPF - EIGRP supports only MD5 authentication. Set the mode to MD5, even though it's the default mode on most devices.
This is an example of Frame relay P2P Interface and EIGRP authentication
interface Serial4/1.25 point-to-point
ip address 134.12.122.2 255.255.255.0
ip authentication mode eigrp 100 md5
ip authentication key-chain eigrp 100 EIGRP_CHAIN
frame-relay interface-dlci 201
end
EIGRP: Maximum Hops
Another attribut that can be useful for controlling the routes is the "maximum-hops". To see each routes hop count:
#show ip route 172.28.185.0
Known via "eigrp 100", distance 90, metric 2297856, type internal
Redistributing via eigrp 100
Last update from 131.1.12.2 on Serial1/0.12, 00:13:47 ago
Routing Descriptor Blocks:
* 131.1.12.2, from 131.1.12.2, 00:13:47 ago, via Serial1/0.12
Route metric is 2297856, traffic share count is 1
Total delay is 25000 microseconds, minimum bandwidth is 1544 Kbit
Reliability 255/255, minimum MTU 1500 bytes
Loading 1/255, Hops 12 <-- 12 HOPS TO THIS ROUTE!!!
To change the Maximum number of Hops to, for example, 10 (Its 100 by Default):
Cisqueros_1(config-router)#metric maximum-hops 10
EIGRP Administrative Distance
By default EIGRP has the following Administrative Distance values:
170 - External EIGRP Routes
90 - Internal EIGRP Routes
5 - EIGRP Summary Routes
You can make EIGRP External routes smaller if you need them to not be less prefered then, for example, OSPF, that has AD 110 for External routes:
Cisqueros_1(config-router)#distance eigrp 90 100
EIGRP Unequal Load Balancing - "variance" command
VARIANCE Command
Variance is a EIGRP feature that enables UNEQUAL load balancing. The only condition that needs to be met is: Paths need to be in the routing table and MEAT THE FEASIBILITY CONDITION!
(Routes ADVERTISED Distance must be lower then the local routes Feasable Distance)
Its configured in the EIGRP configuration mode:
(config-router)#variance 2
This means that it will include the routes with the metric value up to 2 times greater then the Best Route metric.
EIGRP: Route Summarization
The EIGRP route summarization is done exactly the same like RIP summarization, which makes sense because both protocols have the Distance Vector nature. It can also be done on ANY of the routers within the same EIGRP process, unlike the Link State protocols. It's done on the Interface using the command:
R2(config-if)#ip summary-address eigrp 100 3.0.0.0 255.0.0.0
And dont be afraid when you see the following message:
*Apr 27 12:53:32.203: %DUAL-5-NBRCHANGE: EIGRP-IPv4 100: Neighbor 10.1.12.1 (Serial1/0) is resync: summary configured
The interface towards Null0 Interface is created automatically. So dont worry, because EIGRP adds this ""discard route" for Loop Avoidance.
Check if "it worked":
R2#show ip route | i summ
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
D 3.0.0.0/8 is a summary, 00:02:52, Null0
EIGRP Leak Maps
If you wish to have greater granular control the solution presented since 12.3(13) is - the LEAK MAP
If the Leak Map is configured, and:
- It references a non-existing Route Map - The summary route is advertised, more specific routes are suppressed
- If the Route Map however exists, and references a non-existing ACCESS LIST - both the summary route and the more specific routes are advertised
- If the Access List also exists - it lets us define the routes that will be advertised IN ADDITION to the Summarized Route!
To configure the Leak Map just attach a route-map to the "eigrp summary" command:
R2(config-if)#ip summary-address eigrp 100 2.2.4.0 255.255.252.0 leak-map ROUTE_MAP
EIGRP Default Gateway
The command we all know from OSPF and BGP "default-information originate [always]" will not work in EIGRP. Instead we need to:
Option 1: Configure the static route and redistribute it into the EIGRP
Option 2: Summarize the routes into a Default Route using the previously described summarization method (leak map is added if we wish to inject another routes besides the default route)
R2(config-if)#ip summary-address eigrp 100 0.0.0.0 0.0.0.0 [leak-map ROUTE_MAP]
EIGRP: Timers, k-values, "neighbor" command
EIGRP Timers
The EIGRP timers are configured (a bit non-intuitive commands from my point of view) on the interface towards the EIGRP neighbor:
Set the Hello timer for the EIGRP 100 process:
(config-if)#ip hello-interval eigrp 100 30
Set the Dead timer for the EIGRP 100 process:
(config-if)#ip hold-time eigrp 100 120
Check the configured Timers using the command:
#show ip eigrp interface static
EIGRP "show neighbors" command
Cisqueros1#show ip eigrp neighbors
EIGRP-IPv4 Neighbors for AS(100)
H Address Interface Hold Uptime SRTT RTO Q Seq
(sec) (ms) Cnt Num
0 10.1.12.2 Se1/0.12 115 00:10:04 26 200 0 32
How to interpret this output:
H - The order in which neighbors were found, starting from 0
Address - Neighbors IP
Interface - from where we see the Neighbor
Holdtime - how long we have left before we declare the neighbor down (if no Hello is received)
Uptime - How long since we first found out about the neighbor
SRTT - Smooth Round Trip Time. time required for EIGRP packet to reach the neighbor and receive the ACK
RTO - Retransmission Timeout - how long before the packet is re-transmitted
Q Count - Number of packets in the EIGRP queue
SeqNum - Sequence Number of the last received EIGRP packet
EIGRP Metric - K Values
5 K-Values are used to calculate the EIGRP Metric. It´s pretty important to know at least which one is which of the K values:
K1 - Bandwidt
K2 - Load
K3 - Delay
K4 - Reliability
K5 - Reliability
Metric = (K1*BW + (K2*BW)/(256-Load) + K3*Delay) * 256
By default K2 = K4 = K5 = 0, so the Metric depends on the Bandwidth and Delay only
If you need the EIGRP Metric to depend on some other values the command is (ToS should be left 0):
(config-router)#metric weight tos k1 k2 k3 k4 k5
¡¡¡BE CAREFULL BECAUSE K VALUES NEED TO MATCH BETWEEN THE EIGRP NEIGHBORS!!!
RIP: Offset Lists and Update Control
RIP offset list - used to INCREASE the Hop Count. To implement:
- define the ACL defining the relevant routes
- set the Hop Count to be increased (by 13 in this case):
(config-router)#offset-list ACCESS_LIST out 13 Fa0/0
!!! Offset Lists work only with RIP and EIGRP
RIP Updates Source Address Control
RIP Validates the source of the Update packets, so they need to be from the same subnet. If they are not, you can force the route updates by turning off the Source IP Validation:
(config-router)#no validate-update-source
*This way the RIP routes will be exchanged, but if the L3 Reachability is not established between the routers - the RIP routes will not be reachable.
If you need to define the exact sources you want to receive the RIP Updates from - use the "gateway" word on a distribute-list:
(config-router)#distribute-list PREFIX_LIST_WITH_UPDATE_PREFIXES gateway PREFIX_LIST_WITH_UPDATE_SOURCES in Fa0/0
If you need to send the Updates only when something changes in the topology (triggered Updates), there is an Interface command "ip rip triggered":
(config-if)#ip rip triggered
RIP Irregularities: Authentication, Updates: Uni-cast vs Multicast vs Broadcast
RIP (IPv4 versions) is a bit obsolete, I know, and very few production environments will use it as a "routing protocol of choice", but it´s also quite simple and there is simply no excuse for a Network Engineer to not know it in smallest details, let´s say - just in case.
If you need details about the protocol itself, look it up on Wikipedia, or even better - the RFCs:
RIPv1
RIPv2
Here I will only talk about the non-standard RIP behaviors.
RIPv2 weird behavior 1: Authentication
RIP Version 2 supports clear text and MD5 Authentication. The key-chain needs to be defined, and applied to the physical interface using the command:
(config-if)#ip rip authentication mode md5
(config-if)#ip rip authentication key-chain CISQUEROS_CHAIN
IMPORTANT!!!
The passwords and the key numbers MUST be the same on all the routers.
In case the key numbers are different:
- Router with the HIGHER key number will receive ALL the routes
- Router with the LOWER key number will IGNORE (reject) the received all routes received from the other router
RIPv2 weird behavior 2: Updates
By default Version 1 uses Broadcast to send it´s updates. Version 2 uses Multicast, with the destination address 224.0.0.9.
There is a way to "force" the routing updates to only one of the neighbours. To achieve this you need to:
- Manualy define the neighbour using the "network" command
- Define the interface towards the defined neighbour as PASSIVE, to prevent the Multicast Updates that are sent by default (If the interface is not defined as passive, both UNICAST and MULTICAST Updates will be sent)
There is also a way to force Broadcast Updates (ip 255.255.255.255 instead of default multicast destination 224.0.0.9) in Version 2 of RIP, and it´s achieved using the Interface Command:
(config-if)#ip rip v2-broadcast
RIPv2 weird behavior 3: Inject a Default Route into RIP
Another RIP-specific feature is injecting the default route using the "ip default-network" command. This is done in the Global Configuration mode:
(config)#ip default-network 4.0.0.0
Dont forget to advertise the network into RIP protocol:
(config-router)#network 4.0.0.0
Top Interview Questions for Network Engineers, Part 2
The continuation of the previous post, stolen from router-switch.com Blog
Q51. What are the data units at different layers of the TCP / IP protocol site?
Ans. The data unit created at the application layer is called a message, at the transport layer the data unit created is called either a segment or an user datagram, at the network layer the data unit created is called the datagram, at the data link layer the datagram is encapsulated in to a frame and finally transmitted as signals along the transmission media.
Q52. What is Project 802?
Ans. It is a project started by IEEE to set standards that enable intercommunication between equipment from a variety of manufacturers. It is a way for specifying functions of the physical layer, the data link layer and to some extent the network layer to allow for interconnectivity of major LAN protocols.
It consists of the following:
802.1 is an internetworking standard for compatibility of different LANs and MANs across protocols.
802.2 Logical link control (LLC) is the upper sublayer of the data link layer which is non-architecture-specific, that is remains the same for all IEEE-defined LANs.
Media access control (MAC) is the lower sublayer of the data link layer that contains some distinct modules each carrying proprietary information specific to the LAN product being used. The modules are Ethernet LAN (802.3), Token ring LAN (802.4), Token bus LAN (802.5).
802.6 is distributed queue dual bus (DQDB) designed to be used in MANs.
Q53. What is Bandwidth?
Ans. Every line has an upper limit and a lower limit on the frequency of signals it can carry. This limited range is called the bandwidth.
Q54. Difference between bit rate and baud rate.
Ans. Bit rate is the number of bits transmitted during one second whereas baud rate refers to the number of signal units per second that are required to represent those bits.
baud rate = bit rate / N where N is no-of-bits represented by each signal shift.
Q55. What is MAC address?
Ans. The address for a device as it is identified at the Media Access Control (MAC) layer in the network architecture. MAC address is usually stored in ROM on the network adapter card and is unique.
Q56. What is attenuation?
Ans. The degeneration of a signal over distance on a network cable is called attenuation.
Q57. What is cladding?
Ans. A layer of a glass surrounding the center fiber of glass inside a fiber-optic cable.
Q58. What is RAID?
Ans. A method for providing fault tolerance by using multiple hard disk drives.
Q59. What is NETBIOS and NETBEUI?
Ans. NETBIOS is a programming interface that allows I/O requests to be sent to and received from a remote computer and it hides the networking hardware from applications.
NETBEUI is NetBIOS extended user interface. A transport protocol designed by microsoft and IBM for the use on small subnets.
Q60. What is redirector?
Ans. Redirector is software that intercepts file or prints I/O requests and translates them into network requests. This comes under presentation layer.
Q61. What is Beaconing?
Ans. The process that allows a network to self-repair networks problems. The stations on the network notify the other stations on the ring when they are not receiving the transmissions. Beaconing is used in Token ring and FDDI networks.
Q62. What is terminal emulation, in which layer it comes?
Ans. Telnet is also called as terminal emulation. It belongs to application layer.
Q63. What is frame relay, in which layer it comes?
Ans. Frame relay is a packet switching technology. It will operate in the data link layer.
Q64. What do you meant by “triple X” in Networks?
Ans. The function of PAD (Packet Assembler Disassembler) is described in a document known as X.3. The standard protocol has been defined between the terminal and the PAD, called X.28; another standard protocol exists between hte PAD and the network, called X.29. Together, these three recommendations are often called “triple X”
Q65. What is SAP?
Ans. Series of interface points that allow other computers to communicate with the other layers of network protocol stack.
Q66. What is subnet?
Ans. A generic term for section of a large networks usually separated by a bridge or router.
Q67. What is Brouter?
Ans. Hybrid devices that combine the features of both bridges and routers.
Q68. How Gateway is different from Routers?
Ans. A gateway operates at the upper levels of the OSI model and translates information between two completely different network architectures or data formats.
Q69. What are the different type of networking / internetworking devices?
Ans. Repeater:
Also called a regenerator, it is an electronic device that operates only at physical layer. It receives the signal in the network before it becomes weak, regenerates the original bit pattern and puts the refreshed copy back in to the link.
Bridges:
These operate both in the physical and data link layers of LANs of same type. They divide a larger network in to smaller segments. They contain logic that allow them to keep the traffic for each segment separate and thus are repeaters that relay a frame only the side of the segment containing the intended recipent and control congestion.
Routers:
They relay packets among multiple interconnected networks (i.e. LANs of different type). They operate in the physical, data link and network layers. They contain software that enable them to determine which of the several possible paths is the best for a particular transmission.
Gateways:
They relay packets among networks that have different protocols (e.g. between a LAN and a WAN). They accept a packet formatted for one protocol and convert it to a packet formatted for another protocol before forwarding it. They operate in all seven layers of the OSI model.
Q70. What is mesh network?
Ans. A network in which there are multiple network links between computers to provide multiple paths for data to travel.
Q71. What is passive topology?
Ans. When the computers on the network simply listen and receive the signal, they are referred to as passive because they don’t amplify the signal in any way. Example for passive topology – linear bus.
Q72. What are the important topologies for networks?
Ans. BUS topology:
In this each computer is directly connected to primary network cable in a single line.
Advantages:
Inexpensive, easy to install, simple to understand, easy to extend.
STAR topology:
In this all computers are connected using a central hub.
Advantages:
Can be inexpensive, easy to install and reconfigure and easy to trouble shoot physical problems.
RING topology:
In this all computers are connected in loop.
Advantages:
All computers have equal access to network media, installation can be simple, and signal does not degrade as much as in other topologies because each computer regenerates it.
Q73. What are major types of networks and explain Server-based network and Peer-to-peer network.
Ans. Peer-to-peer network, computers can act as both servers sharing resources and as clients using the resources.
Server-based networks provide centralized control of network resources and rely on server computers to provide security and network administration
Q74. What is Protocol Data Unit?
Ans. The data unit in the LLC level is called the protocol data unit (PDU). The PDU contains of four fields a destination service access point (DSAP), a source service access point (SSAP), a control field and an information field. DSAP, SSAP are addresses used by the LLC to identify the protocol stacks on the receiving and sending machines that are generating and using the data. The control field specifies whether the PDU frame is a information frame (I -frame) or a supervisory frame (S – frame) or a unnumbered frame (U – frame).
Q75. What is difference between baseband and broadband transmission?
Ans. In a baseband transmission, the entire bandwidth of the cable is consumed by a single signal. In broadband transmission, signals are sent on multiple frequencies, allowing multiple signals to be sent simultaneously.
Q76. What are the possible ways of data exchange?
Ans. (i) Simplex (ii) Half-duplex (iii) Full-duplex.
Q77. What are the types of Transmission media?
Ans. Signals are usually transmitted over some transmission media that are broadly classified in to two categories.
Guided Media:
These are those that provide a conduit from one device to another that include twisted-pair, coaxial cable and fiber-optic cable. A signal traveling along any of these media is directed and is contained by the physical limits of the medium. Twisted-pair and coaxial cable use metallic that accept and transport signals in the form of electrical current. Optical fiber is a glass or plastic cable that accepts and transports signals in the form of light.
Unguided Media:
This is the wireless media that transport electromagnetic waves without using a physical conductor. Signals are broadcast either through air. This is done through radio communication, satellite communication and cellular telephony.
Q78. Difference between the communication and transmission.
Ans. Transmission is a physical movement of information and concern issues like bit polarity, synchronization, clock etc.
Communication means the meaning full exchange of information between two communication media.
Q79.The Internet Control Message Protocol occurs at what layer of the seven layer model?
Ans. Network
Q80.Which protocol resolves an IP address to a MAC address?
Ans. ARP
Q81.MIDI and MPEG are examples of what layer of the OSI seven layer model?
Ans. Presentation
Q82.What is the protocol number for UDP?
Ans. 17
Q83.Which protocol is used for booting diskless workstations?
Ans. RARP
Q84.Which layer is responsible for putting 1s and 0s into a logical group?
Ans. Physical
Q85.What does ‘P’ mean when running a Trace?
Ans. Protocol unreachable
Q86.UDP works at which layer of the DOD model?
Ans. Host to Host
Q87.What is the default encapsulation of Netware 3.12?
Ans. 802.2
Q88.Ping uses which Internet layer protocol?
Ans. ICMP
Q89.Which switching technology can reduce the size of a broadcast domain?
Ans. VLAN
Q90.What is the first step in data encapsulation?
Ans. User information is converted into data.
Q91.What is the protocol number for TCP?
Ans. 6
Q92.What do you use the Aux port for?
Ans. Modem
Q93.Repeaters work at which layer of the OSI model?
Ans. Physical
Q94.WAN stands for which of the following?
Ans. Wide Area Network
Q95.What ISDN protocol specifies concepts, terminology, and services?
Q96.LAN stands for which of the following?
Ans. Local Area Network
Q97.DHCP stands for
Ans. Dynamic Host Configuration Protocol
Q98.What does the acronym ARP stand for?
Ans. Address Resolution Protocol
Q99.Which layer is responsible for identifying and establishing the availability of the intended communication partner?
Ans. Application.
Q100.Which OSI layer provides mechanical, electrical, procedural for activating, maintaining physical link?
Ans. Physical.
Q51. What are the data units at different layers of the TCP / IP protocol site?
Ans. The data unit created at the application layer is called a message, at the transport layer the data unit created is called either a segment or an user datagram, at the network layer the data unit created is called the datagram, at the data link layer the datagram is encapsulated in to a frame and finally transmitted as signals along the transmission media.
Q52. What is Project 802?
Ans. It is a project started by IEEE to set standards that enable intercommunication between equipment from a variety of manufacturers. It is a way for specifying functions of the physical layer, the data link layer and to some extent the network layer to allow for interconnectivity of major LAN protocols.
It consists of the following:
802.1 is an internetworking standard for compatibility of different LANs and MANs across protocols.
802.2 Logical link control (LLC) is the upper sublayer of the data link layer which is non-architecture-specific, that is remains the same for all IEEE-defined LANs.
Media access control (MAC) is the lower sublayer of the data link layer that contains some distinct modules each carrying proprietary information specific to the LAN product being used. The modules are Ethernet LAN (802.3), Token ring LAN (802.4), Token bus LAN (802.5).
802.6 is distributed queue dual bus (DQDB) designed to be used in MANs.
Q53. What is Bandwidth?
Ans. Every line has an upper limit and a lower limit on the frequency of signals it can carry. This limited range is called the bandwidth.
Q54. Difference between bit rate and baud rate.
Ans. Bit rate is the number of bits transmitted during one second whereas baud rate refers to the number of signal units per second that are required to represent those bits.
baud rate = bit rate / N where N is no-of-bits represented by each signal shift.
Q55. What is MAC address?
Ans. The address for a device as it is identified at the Media Access Control (MAC) layer in the network architecture. MAC address is usually stored in ROM on the network adapter card and is unique.
Q56. What is attenuation?
Ans. The degeneration of a signal over distance on a network cable is called attenuation.
Q57. What is cladding?
Ans. A layer of a glass surrounding the center fiber of glass inside a fiber-optic cable.
Q58. What is RAID?
Ans. A method for providing fault tolerance by using multiple hard disk drives.
Q59. What is NETBIOS and NETBEUI?
Ans. NETBIOS is a programming interface that allows I/O requests to be sent to and received from a remote computer and it hides the networking hardware from applications.
NETBEUI is NetBIOS extended user interface. A transport protocol designed by microsoft and IBM for the use on small subnets.
Q60. What is redirector?
Ans. Redirector is software that intercepts file or prints I/O requests and translates them into network requests. This comes under presentation layer.
Q61. What is Beaconing?
Ans. The process that allows a network to self-repair networks problems. The stations on the network notify the other stations on the ring when they are not receiving the transmissions. Beaconing is used in Token ring and FDDI networks.
Q62. What is terminal emulation, in which layer it comes?
Ans. Telnet is also called as terminal emulation. It belongs to application layer.
Q63. What is frame relay, in which layer it comes?
Ans. Frame relay is a packet switching technology. It will operate in the data link layer.
Q64. What do you meant by “triple X” in Networks?
Ans. The function of PAD (Packet Assembler Disassembler) is described in a document known as X.3. The standard protocol has been defined between the terminal and the PAD, called X.28; another standard protocol exists between hte PAD and the network, called X.29. Together, these three recommendations are often called “triple X”
Q65. What is SAP?
Ans. Series of interface points that allow other computers to communicate with the other layers of network protocol stack.
Q66. What is subnet?
Ans. A generic term for section of a large networks usually separated by a bridge or router.
Q67. What is Brouter?
Ans. Hybrid devices that combine the features of both bridges and routers.
Q68. How Gateway is different from Routers?
Ans. A gateway operates at the upper levels of the OSI model and translates information between two completely different network architectures or data formats.
Q69. What are the different type of networking / internetworking devices?
Ans. Repeater:
Also called a regenerator, it is an electronic device that operates only at physical layer. It receives the signal in the network before it becomes weak, regenerates the original bit pattern and puts the refreshed copy back in to the link.
Bridges:
These operate both in the physical and data link layers of LANs of same type. They divide a larger network in to smaller segments. They contain logic that allow them to keep the traffic for each segment separate and thus are repeaters that relay a frame only the side of the segment containing the intended recipent and control congestion.
Routers:
They relay packets among multiple interconnected networks (i.e. LANs of different type). They operate in the physical, data link and network layers. They contain software that enable them to determine which of the several possible paths is the best for a particular transmission.
Gateways:
They relay packets among networks that have different protocols (e.g. between a LAN and a WAN). They accept a packet formatted for one protocol and convert it to a packet formatted for another protocol before forwarding it. They operate in all seven layers of the OSI model.
Q70. What is mesh network?
Ans. A network in which there are multiple network links between computers to provide multiple paths for data to travel.
Q71. What is passive topology?
Ans. When the computers on the network simply listen and receive the signal, they are referred to as passive because they don’t amplify the signal in any way. Example for passive topology – linear bus.
Q72. What are the important topologies for networks?
Ans. BUS topology:
In this each computer is directly connected to primary network cable in a single line.
Advantages:
Inexpensive, easy to install, simple to understand, easy to extend.
STAR topology:
In this all computers are connected using a central hub.
Advantages:
Can be inexpensive, easy to install and reconfigure and easy to trouble shoot physical problems.
RING topology:
In this all computers are connected in loop.
Advantages:
All computers have equal access to network media, installation can be simple, and signal does not degrade as much as in other topologies because each computer regenerates it.
Q73. What are major types of networks and explain Server-based network and Peer-to-peer network.
Ans. Peer-to-peer network, computers can act as both servers sharing resources and as clients using the resources.
Server-based networks provide centralized control of network resources and rely on server computers to provide security and network administration
Q74. What is Protocol Data Unit?
Ans. The data unit in the LLC level is called the protocol data unit (PDU). The PDU contains of four fields a destination service access point (DSAP), a source service access point (SSAP), a control field and an information field. DSAP, SSAP are addresses used by the LLC to identify the protocol stacks on the receiving and sending machines that are generating and using the data. The control field specifies whether the PDU frame is a information frame (I -frame) or a supervisory frame (S – frame) or a unnumbered frame (U – frame).
Q75. What is difference between baseband and broadband transmission?
Ans. In a baseband transmission, the entire bandwidth of the cable is consumed by a single signal. In broadband transmission, signals are sent on multiple frequencies, allowing multiple signals to be sent simultaneously.
Q76. What are the possible ways of data exchange?
Ans. (i) Simplex (ii) Half-duplex (iii) Full-duplex.
Q77. What are the types of Transmission media?
Ans. Signals are usually transmitted over some transmission media that are broadly classified in to two categories.
Guided Media:
These are those that provide a conduit from one device to another that include twisted-pair, coaxial cable and fiber-optic cable. A signal traveling along any of these media is directed and is contained by the physical limits of the medium. Twisted-pair and coaxial cable use metallic that accept and transport signals in the form of electrical current. Optical fiber is a glass or plastic cable that accepts and transports signals in the form of light.
Unguided Media:
This is the wireless media that transport electromagnetic waves without using a physical conductor. Signals are broadcast either through air. This is done through radio communication, satellite communication and cellular telephony.
Q78. Difference between the communication and transmission.
Ans. Transmission is a physical movement of information and concern issues like bit polarity, synchronization, clock etc.
Communication means the meaning full exchange of information between two communication media.
Q79.The Internet Control Message Protocol occurs at what layer of the seven layer model?
Ans. Network
Q80.Which protocol resolves an IP address to a MAC address?
Ans. ARP
Q81.MIDI and MPEG are examples of what layer of the OSI seven layer model?
Ans. Presentation
Q82.What is the protocol number for UDP?
Ans. 17
Q83.Which protocol is used for booting diskless workstations?
Ans. RARP
Q84.Which layer is responsible for putting 1s and 0s into a logical group?
Ans. Physical
Q85.What does ‘P’ mean when running a Trace?
Ans. Protocol unreachable
Q86.UDP works at which layer of the DOD model?
Ans. Host to Host
Q87.What is the default encapsulation of Netware 3.12?
Ans. 802.2
Q88.Ping uses which Internet layer protocol?
Ans. ICMP
Q89.Which switching technology can reduce the size of a broadcast domain?
Ans. VLAN
Q90.What is the first step in data encapsulation?
Ans. User information is converted into data.
Q91.What is the protocol number for TCP?
Ans. 6
Q92.What do you use the Aux port for?
Ans. Modem
Q93.Repeaters work at which layer of the OSI model?
Ans. Physical
Q94.WAN stands for which of the following?
Ans. Wide Area Network
Q95.What ISDN protocol specifies concepts, terminology, and services?
Q96.LAN stands for which of the following?
Ans. Local Area Network
Q97.DHCP stands for
Ans. Dynamic Host Configuration Protocol
Q98.What does the acronym ARP stand for?
Ans. Address Resolution Protocol
Q99.Which layer is responsible for identifying and establishing the availability of the intended communication partner?
Ans. Application.
Q100.Which OSI layer provides mechanical, electrical, procedural for activating, maintaining physical link?
Ans. Physical.
Top Interview Questions for Network Engineers, Part 1
This was originally posted by another blog, router-switch.com and I must say that agree only partially. Some questions are too deep, but not related to Networks exactly, but more to the Systems part, while the purely Networking questions are not so deep. No-one who´s looking for an actual Network Engineer will ask you "What is OSPF?" Still, I enjoyed browsing through it, and it might be true - Network/Systems engineer should know all this...
Q1. What are 10Base2, 10Base5 and 10BaseT Ethernet LANs?
Ans. 10Base2—An Ethernet term meaning a maximum transfer rate of 10 Megabits per second that uses baseband signaling, with a contiguous cable segment length of 100 meters and a maximum of 2 segments.
10Base5—An Ethernet term meaning a maximum transfer rate of 10 Megabits per second that uses baseband signaling, with 5 continuous segments not exceeding 100 meters per segment.
10BaseT—An Ethernet term meaning a maximum transfer rate of 10 Megabits per second that uses baseband signaling and twisted pair cabling.
Q2. What is the difference between an unspecified passive open and a fully specified passive open?
Ans. An unspecified passive open has the server waiting for a connection request from a client. A fully specified passive open has the server waiting for a connection from a specific client.
Q3. Explain the function of Transmission Control Block.
Ans. A TCB is a complex data structure that contains a considerable amount of information about each connection.
Q4. What is a Management Information Base (MIB)?
Ans. A Management Information Base is part of every SNMP-managed device. Each SNMP agent has the MIB database that contains information about the device’s status, its performance, connections, and configuration. The MIB is queried by SNMP.
Q5. What is anonymous FTP and why would you use it?
Ans. Anonymous FTP enables users to connect to a host without using a valid login and password. Usually, anonymous FTP uses a login called anonymous or guest, with the password usually requesting the user’s ID for tracking purposes only. Anonymous FTP is used to enable a large number of users to access files on the host without having to go to the trouble of setting up logins for them all. Anonymous FTP systems usually have strict controls over the areas an anonymous user can access.
Q6. What is a pseudo tty?
Ans. A pseudo tty or false terminal enables external machines to connect through Telnet or rlogin. Without a pseudo tty, no connection can take place.
Q7. Which layer of the 7 layer model provides services to the Application layer over the Session layer connection?
Ans. Presentation.
Q8. What does the Mount protocol do?
Ans. The Mount protocol returns a file handle and the name of the file system in which a requested file resides. The message is sent to the client from the server after reception of aclient’s request.
Q9. What is External Data Representation?
Ans. External Data Representation is a method of encoding data within an RPC message, used to ensure that the data is not system-dependent.
Q10. Which OSI Reference Layer controls application to application communication?
Ans. Session
Q11. BOOTP helps a diskless workstation boot. How does it get a message to the network looking for its IP address and the location of its operating system boot files ?
Ans. BOOTP sends a UDP message with a subnetwork broadcast address and waits for a reply from a server that gives it the IP address. The same message might contain the name of the machine that has the boot files on it. If the boot image location is not specified, the workstation sends another UDP message to query the server.
Q12. What is a DNS resource record?
Ans. A resource record is an entry in a name server’s database. There are several types of resource records used, including name-to-address resolution information. Resource records are maintained as ASCII files.
Q13. What protocol is used by DNS name servers?
Ans. DNS uses UDP for communication between servers. It is a better choice than TCP because of the improved speed a connectionless protocol offers. Of course, transmission reliability suffers with UDP.
Q14. What is the difference between interior and exterior neighbor gateways?
Ans. Interior gateways connect LANs of one organization, whereas exterior gateways connect the organization to the outside world.
Q15. What is the HELLO protocol used for?
Ans. The HELLO protocol uses time instead of distance to determine optimal routing. It is an alternative to the Routing Information Protocol.
Q16. What are the advantages and disadvantages of the three types of routing tables?
Ans. The three types of routing tables are fixed, dynamic, and fixed central. The fixed table must be manually modified every time there is a change. A dynamic table changes its information based on network traffic, reducing the amount of manual maintenance. A fixed central table lets a manager modify only one table, which is then read by other devices. The fixed central table reduces the need to update each machine’s table, as with the fixed table. Usually a dynamic table causes the fewest problems for a network administrator, although the table’s contents can change without the administrator being aware of the change.
Q17. What is a characteristic of Store and Forward switches?
Ans. They read the entire frame and check CRC before forwarding.
Q18. What is source route?
Ans. It is a sequence of IP addresses identifying the route a datagram must follow. A source route may optionally be included in an IP datagram header.
Q19. What is RIP (Routing Information Protocol)?
Ans. It is a simple protocol used to exchange information between the routers.
Q20. What is SLIP (Serial Line Interface Protocol)?
Ans. It is a very simple protocol used for transmission of IP datagrams across a serial line.
Q21. What is Proxy ARP?
Ans. It is using a router to answer ARP requests. This will be done when the originating host believes that a destination is local, when in fact is lies beyond router.
Q22. What is OSPF?
Ans. It is an Internet routing protocol that scales well, can route traffic along multiple paths, and uses knowledge of an Internet’s topology to make accurate routing decisions.
Q23. What is Kerberos?
Ans. It is an authentication service developed at the Massachusetts Institute of Technology. Kerberos uses encryption to prevent intruders from discovering passwords and gaining unauthorized access to files.
Q24. What is a Multi-homed Host?
Ans. It is a host that has a multiple network interfaces and that requires multiple IP addressesis called as a Multi-homed Host.
Q25. What is NVT (Network Virtual Terminal)?
Ans. It is a set of rules defining a very simple virtual terminal interaction. The NVT is used in the start of a Telnet session.
Q26. What is Gateway-to-Gateway protocol?
Ans. It is a protocol formerly
used to exchange routing information between Internet core routers.
Q27. What is BGP (Border Gateway Protocol)?
Ans. It is a protocol used to advertise the set of networks that can be reached with in an autonomous system. BGP enables this information to be shared with the autonomous system. This is newer than EGP (Exterior Gateway Protocol).
Q28. What is autonomous system?
Ans. It is a collection of routers under the control of a single administrative authority and that uses a common Interior Gateway Protocol.
Q29. What is EGP (Exterior Gateway Protocol)?
Ans. It is the protocol the routers in neighboring autonomous systems use to identify the set of networks that can be reached within or via each autonomous system.
Q30. What is IGP (Interior Gateway Protocol)?
Ans. It is any routing protocol used within an autonomous system.
Q31. What is Mail Gateway?
Ans. It is a system that performs a protocol translation between different electronic mail deliveryprotocols.
Q32. What is wide-mouth frog?
Ans. Wide-mouth frog is the simplest known key distribution center (KDC) authentication protocol.
Q33. What are Digrams and Trigrams?
Ans. The most common two letter combinations are called as digrams. e.g. th, in, er, re and an. The most common three letter combinations are called as trigrams. e.g. the, ing, and, and ion.
Q34. What is silly window syndrome?
Ans. It is a problem that can ruin TCP performance. This problem occurs when data are passed to the sending TCP entity in large blocks, but an interactive application on the receiving side reads 1 byte at a time.
Q35. What is region?
Ans. When hierarchical routing is used, the routers are divided into what we call regions, with each router knowing all the details about how to route packets to destinations within its own region, but knowing nothing about the internal structure of other regions.
Q36. What is multicast routing?
Ans. Sending a message to a group is called multicasting, and its routing algorithm is called multicast routing.
Q37. What is traffic shaping?
Ans. One of the main causes of congestion is that traffic is often busy. If hosts could be made to transmit at a uniform rate,congestion would be less common. Another open loop method to help manage congestion is forcing the packet to be transmitted at a more predictable rate. This is called traffic shaping.
Q38. What is packet filter?
Ans. Packet filter is a standard router equipped with some extra functionality. The extra functionality allows every incoming or outgoing packet to be inspected. Packets meeting some criterion are forwarded normally. Those that fail the test are dropped.
Q39. What is virtual path?
Ans. Along any transmission path from a given source to a given destination, a group of virtual circuits can be grouped together into what is called path.
Q40. What is virtual channel?
Ans. Virtual channel is normally a connection from one source to one destination, although multicast connections are also permitted. The other name for virtual channel is virtual circuit.
Q41. What is logical link control?
Ans. One of two sublayers of the data link layer of OSI reference model, as defined by the IEEE 802 standard. This sublayer is responsible for maintaining the link between computers when they are sending data across the physical network connection.
Q42. Why should you care about the OSI Reference Model?
Ans. It provides a framework for discussing network operations and design.
Q43. What is the difference between routable and non- routable protocols?
Ans. Routable protocols can work with a router and can be used to build large networks. Non-Routable protocols are designed to work on small, local networks and cannot be used with a router.
Q44. What is MAU?
Ans. In token Ring , hub is called Multistation Access Unit(MAU).
Q45. Explain 5-4-3 rule?
Ans. In a Ethernet network, between any two points on the network, there can be no more than five network segments or four repeaters, and of those five segments only three of segments can be populated.
Q46. What is the difference between TFTP and FTP application layer protocols?
Ans. The Trivial File Transfer Protocol (TFTP) allows a local host to obtain files from a remote host but does not provide reliability or security. It uses the fundamental packet delivery services offered by UDP. The File Transfer Protocol (FTP) is the standard mechanism provided by TCP / IP for copying a file from one host to another. It uses the services offered by TCP and so is reliable and secure. It establishes two connections (virtual circuits) between the hosts, one for data transfer and another for control information.
Q47. What is the range of addresses in the classes of internet addresses?
Ans. Class A 0.0.0.0 – 127.255.255.255
Class B 128.0.0.0 – 191.255.255.255
Class C 192.0.0.0 – 223.255.255.255
Class D 224.0.0.0 – 239.255.255.255
Class E 240.0.0.0 – 247.255.255.255
Q48. What is the minimum and maximum length of the header in the TCP segment and IP datagram?
Ans. The header should have a minimum length of 20 bytes and can have a maximum length of 60 bytes.
Q49. What is difference between ARP and RARP?
Ans. The address resolution protocol (ARP) is used to associate the 32 bit IP address with the 48 bit physical address, used by a host or a router to find the physical address of another host on its network by sending a ARP query packet that includes the IP address of the receiver. The reverse address resolution protocol (RARP) allows a host to discover its Internet address when it knows only its physical address.
Q50. What is ICMP?
Ans. ICMP is Internet Control Message Protocol, a network layer protocol of the TCP/IP suite used by hosts and gateways to send notification of datagram problems back to the sender. It uses the echo test / reply to test whether a destination is reachable and responding. It also handles both control and error messages.
Q1. What are 10Base2, 10Base5 and 10BaseT Ethernet LANs?
Ans. 10Base2—An Ethernet term meaning a maximum transfer rate of 10 Megabits per second that uses baseband signaling, with a contiguous cable segment length of 100 meters and a maximum of 2 segments.
10Base5—An Ethernet term meaning a maximum transfer rate of 10 Megabits per second that uses baseband signaling, with 5 continuous segments not exceeding 100 meters per segment.
10BaseT—An Ethernet term meaning a maximum transfer rate of 10 Megabits per second that uses baseband signaling and twisted pair cabling.
Q2. What is the difference between an unspecified passive open and a fully specified passive open?
Ans. An unspecified passive open has the server waiting for a connection request from a client. A fully specified passive open has the server waiting for a connection from a specific client.
Q3. Explain the function of Transmission Control Block.
Ans. A TCB is a complex data structure that contains a considerable amount of information about each connection.
Q4. What is a Management Information Base (MIB)?
Ans. A Management Information Base is part of every SNMP-managed device. Each SNMP agent has the MIB database that contains information about the device’s status, its performance, connections, and configuration. The MIB is queried by SNMP.
Q5. What is anonymous FTP and why would you use it?
Ans. Anonymous FTP enables users to connect to a host without using a valid login and password. Usually, anonymous FTP uses a login called anonymous or guest, with the password usually requesting the user’s ID for tracking purposes only. Anonymous FTP is used to enable a large number of users to access files on the host without having to go to the trouble of setting up logins for them all. Anonymous FTP systems usually have strict controls over the areas an anonymous user can access.
Q6. What is a pseudo tty?
Ans. A pseudo tty or false terminal enables external machines to connect through Telnet or rlogin. Without a pseudo tty, no connection can take place.
Q7. Which layer of the 7 layer model provides services to the Application layer over the Session layer connection?
Ans. Presentation.
Q8. What does the Mount protocol do?
Ans. The Mount protocol returns a file handle and the name of the file system in which a requested file resides. The message is sent to the client from the server after reception of aclient’s request.
Q9. What is External Data Representation?
Ans. External Data Representation is a method of encoding data within an RPC message, used to ensure that the data is not system-dependent.
Q10. Which OSI Reference Layer controls application to application communication?
Ans. Session
Q11. BOOTP helps a diskless workstation boot. How does it get a message to the network looking for its IP address and the location of its operating system boot files ?
Ans. BOOTP sends a UDP message with a subnetwork broadcast address and waits for a reply from a server that gives it the IP address. The same message might contain the name of the machine that has the boot files on it. If the boot image location is not specified, the workstation sends another UDP message to query the server.
Q12. What is a DNS resource record?
Ans. A resource record is an entry in a name server’s database. There are several types of resource records used, including name-to-address resolution information. Resource records are maintained as ASCII files.
Q13. What protocol is used by DNS name servers?
Ans. DNS uses UDP for communication between servers. It is a better choice than TCP because of the improved speed a connectionless protocol offers. Of course, transmission reliability suffers with UDP.
Q14. What is the difference between interior and exterior neighbor gateways?
Ans. Interior gateways connect LANs of one organization, whereas exterior gateways connect the organization to the outside world.
Q15. What is the HELLO protocol used for?
Ans. The HELLO protocol uses time instead of distance to determine optimal routing. It is an alternative to the Routing Information Protocol.
Q16. What are the advantages and disadvantages of the three types of routing tables?
Ans. The three types of routing tables are fixed, dynamic, and fixed central. The fixed table must be manually modified every time there is a change. A dynamic table changes its information based on network traffic, reducing the amount of manual maintenance. A fixed central table lets a manager modify only one table, which is then read by other devices. The fixed central table reduces the need to update each machine’s table, as with the fixed table. Usually a dynamic table causes the fewest problems for a network administrator, although the table’s contents can change without the administrator being aware of the change.
Q17. What is a characteristic of Store and Forward switches?
Ans. They read the entire frame and check CRC before forwarding.
Q18. What is source route?
Ans. It is a sequence of IP addresses identifying the route a datagram must follow. A source route may optionally be included in an IP datagram header.
Q19. What is RIP (Routing Information Protocol)?
Ans. It is a simple protocol used to exchange information between the routers.
Q20. What is SLIP (Serial Line Interface Protocol)?
Ans. It is a very simple protocol used for transmission of IP datagrams across a serial line.
Q21. What is Proxy ARP?
Ans. It is using a router to answer ARP requests. This will be done when the originating host believes that a destination is local, when in fact is lies beyond router.
Q22. What is OSPF?
Ans. It is an Internet routing protocol that scales well, can route traffic along multiple paths, and uses knowledge of an Internet’s topology to make accurate routing decisions.
Q23. What is Kerberos?
Ans. It is an authentication service developed at the Massachusetts Institute of Technology. Kerberos uses encryption to prevent intruders from discovering passwords and gaining unauthorized access to files.
Q24. What is a Multi-homed Host?
Ans. It is a host that has a multiple network interfaces and that requires multiple IP addressesis called as a Multi-homed Host.
Q25. What is NVT (Network Virtual Terminal)?
Ans. It is a set of rules defining a very simple virtual terminal interaction. The NVT is used in the start of a Telnet session.
Q26. What is Gateway-to-Gateway protocol?
Ans. It is a protocol formerly
used to exchange routing information between Internet core routers.
Q27. What is BGP (Border Gateway Protocol)?
Ans. It is a protocol used to advertise the set of networks that can be reached with in an autonomous system. BGP enables this information to be shared with the autonomous system. This is newer than EGP (Exterior Gateway Protocol).
Q28. What is autonomous system?
Ans. It is a collection of routers under the control of a single administrative authority and that uses a common Interior Gateway Protocol.
Q29. What is EGP (Exterior Gateway Protocol)?
Ans. It is the protocol the routers in neighboring autonomous systems use to identify the set of networks that can be reached within or via each autonomous system.
Q30. What is IGP (Interior Gateway Protocol)?
Ans. It is any routing protocol used within an autonomous system.
Q31. What is Mail Gateway?
Ans. It is a system that performs a protocol translation between different electronic mail deliveryprotocols.
Q32. What is wide-mouth frog?
Ans. Wide-mouth frog is the simplest known key distribution center (KDC) authentication protocol.
Q33. What are Digrams and Trigrams?
Ans. The most common two letter combinations are called as digrams. e.g. th, in, er, re and an. The most common three letter combinations are called as trigrams. e.g. the, ing, and, and ion.
Q34. What is silly window syndrome?
Ans. It is a problem that can ruin TCP performance. This problem occurs when data are passed to the sending TCP entity in large blocks, but an interactive application on the receiving side reads 1 byte at a time.
Q35. What is region?
Ans. When hierarchical routing is used, the routers are divided into what we call regions, with each router knowing all the details about how to route packets to destinations within its own region, but knowing nothing about the internal structure of other regions.
Q36. What is multicast routing?
Ans. Sending a message to a group is called multicasting, and its routing algorithm is called multicast routing.
Q37. What is traffic shaping?
Ans. One of the main causes of congestion is that traffic is often busy. If hosts could be made to transmit at a uniform rate,congestion would be less common. Another open loop method to help manage congestion is forcing the packet to be transmitted at a more predictable rate. This is called traffic shaping.
Q38. What is packet filter?
Ans. Packet filter is a standard router equipped with some extra functionality. The extra functionality allows every incoming or outgoing packet to be inspected. Packets meeting some criterion are forwarded normally. Those that fail the test are dropped.
Q39. What is virtual path?
Ans. Along any transmission path from a given source to a given destination, a group of virtual circuits can be grouped together into what is called path.
Q40. What is virtual channel?
Ans. Virtual channel is normally a connection from one source to one destination, although multicast connections are also permitted. The other name for virtual channel is virtual circuit.
Q41. What is logical link control?
Ans. One of two sublayers of the data link layer of OSI reference model, as defined by the IEEE 802 standard. This sublayer is responsible for maintaining the link between computers when they are sending data across the physical network connection.
Q42. Why should you care about the OSI Reference Model?
Ans. It provides a framework for discussing network operations and design.
Q43. What is the difference between routable and non- routable protocols?
Ans. Routable protocols can work with a router and can be used to build large networks. Non-Routable protocols are designed to work on small, local networks and cannot be used with a router.
Q44. What is MAU?
Ans. In token Ring , hub is called Multistation Access Unit(MAU).
Q45. Explain 5-4-3 rule?
Ans. In a Ethernet network, between any two points on the network, there can be no more than five network segments or four repeaters, and of those five segments only three of segments can be populated.
Q46. What is the difference between TFTP and FTP application layer protocols?
Ans. The Trivial File Transfer Protocol (TFTP) allows a local host to obtain files from a remote host but does not provide reliability or security. It uses the fundamental packet delivery services offered by UDP. The File Transfer Protocol (FTP) is the standard mechanism provided by TCP / IP for copying a file from one host to another. It uses the services offered by TCP and so is reliable and secure. It establishes two connections (virtual circuits) between the hosts, one for data transfer and another for control information.
Q47. What is the range of addresses in the classes of internet addresses?
Ans. Class A 0.0.0.0 – 127.255.255.255
Class B 128.0.0.0 – 191.255.255.255
Class C 192.0.0.0 – 223.255.255.255
Class D 224.0.0.0 – 239.255.255.255
Class E 240.0.0.0 – 247.255.255.255
Q48. What is the minimum and maximum length of the header in the TCP segment and IP datagram?
Ans. The header should have a minimum length of 20 bytes and can have a maximum length of 60 bytes.
Q49. What is difference between ARP and RARP?
Ans. The address resolution protocol (ARP) is used to associate the 32 bit IP address with the 48 bit physical address, used by a host or a router to find the physical address of another host on its network by sending a ARP query packet that includes the IP address of the receiver. The reverse address resolution protocol (RARP) allows a host to discover its Internet address when it knows only its physical address.
Q50. What is ICMP?
Ans. ICMP is Internet Control Message Protocol, a network layer protocol of the TCP/IP suite used by hosts and gateways to send notification of datagram problems back to the sender. It uses the echo test / reply to test whether a destination is reachable and responding. It also handles both control and error messages.
CCIE: Lab Exam, what does it look like?
From what I've read the 50% of passing the CCIE is knowledge and speed, and the other 50% is knowing how to organize yourself. So I recently bought the Logitech K200 keyboard, which I heard is the one I will be using when I do the exam in the Busseles testing center. Why a new keyboard? Well, supposedly 8 hours is enough if you know your stuff, but you are having a serious run against the time, so - if I can eliminate any of the possible distracting factor for 7 euros on eBay - right on!
There are A LOT of forum posts about these, but in my opinion one of the most important things is to actually know how the Lab Interface will be. So, here's a YouTube video I recently found about it.
There are A LOT of forum posts about these, but in my opinion one of the most important things is to actually know how the Lab Interface will be. So, here's a YouTube video I recently found about it.
frame relay "map" vs "interface-dlci" and "Inverse ARP"
I remember when I was first getting into Frame Relay I had much trouble getting the concept of DLCIs, LMIs and how it all works, because it´s so much different then other L2-L3 protocols. It took me a while to realize that the concept is quite simple, you just need someone to tell you from which side you should "attack" this technology.
Three main concepts will be explained within this post:
- Frame Relay configuration on a Physical Interface + Inverse ARP
- Frame Relay configuration on a Point-to-Point Sub-interface
- Frame Relay configuration on a Multi-Point Sub-interface
DTE-DCE
There are two possible interface plugs in the Frame Relay cabling: DCE and DTE. I´m not going to go into details here, but what you do need to know as a Network Engineer are two things:
- If the interface is DCE you do need to provide the clocking on that side. Check the type using:
#show controller Serial0/0 | inc Clocks
and if you see "DTE V.35 Tx and Rx clocks detected" you are safe
If you want to FORCE the DCE and provide the clocking:
(config-if) #frame-relay intf-type dce
Inverse ARP
Like a regular ARP (Address Resolution Protocol) the Inverse-ARP is used to map the Layer 2 (DLCI in the case of Frame Relay) and the Layer 3 (IP Address).
When frame-relay is configured in a point-to-point manner there is no need to configure the mapping and the inverseARP is disabled by default.
When you configure the L2-L3 mapping manually, like in the Physical Interface configuration case (Case 1 of this post), you already have the mapping that the ARP provides, so you need to manually disable the inverse ARP.
1. Frame Relay configuration on a Physical Interface
When the Frame Relay configuration is done on a Physical interface, you need to do the following:
- Assign the IP to the interface
(config-if)#ip address 4.2.2.1 255.255.255.0
- Define the encapsulation using the Interface command:
(config-if)#encapsulation frame-relay
- Map the IP Address you want to access to the DLCI you have defined for that particular IP:
(config-if)#frame-relay map ip 4.2.2.2 201 broadcast
* Have in mind that DLCIs are only LOCALLY significant to the Router (DLCI value 201 will mean one thing to one router, and a totally different thing to another)
* "broadcast" is added because the local router will not be sending Broadcasts. The optional broadcast keyword in the frame-relay map command is required if broadcast and multicast traffic are to be sent over the specified dlci. Without the broadcast option, dynamic routing protocols such as EIGRP, OSPF and RIPv2 would not be able to advertise multicast route updates over the specified dlci.
Check the mappings using the following Privileged Mode command:
#show frame-relay map
Disable the inverse ARP (for reasons explained above)
(config-if)#no frame-relay inverse-arp
2. Frame Relay configuration on a Point-to-Point Sub-interface
For both of the following cases Frame-Relay encapsulation needs to be defined first on a Physical Interface bases, and the interface needs to be Administratively "UP". Create the Point to Point sub-interface and assign the IP address:
(config)#interface Serial0/0.12 point-to-point
(config-if)#ip address 4.2.2.1 255.255.255.0
Have in mind that there is no need to create the mapping L2-L3 because there is only one router on the other side of the PVC, so only one DLCI needs to be defined on the interface. For the same reason (L2-L3 mapping already defined) the inverse-ARP is disabled on this kind of sub-interfaces by default.
(config-if)#frame-relay interface-dlci 201
3. Frame Relay configuration on a Multi-Point Sub-interface
Create the Multipoint sub-interface and assign the IP address:
(config)#interface Serial0/0.123 multipoint
(config-if)#ip address 4.2.2.1 255.255.255.0
As there can be various routers on the other side of the PVC, the IP-DLCI mapping needs to be defined:
(config-if)#frame-relay map ip 4.2.2.2 102
(config-if)#frame-relay map ip 4.2.2.3 103
Unlike on the per-physical-interface basis, the inverse ARP doesn't need to be disabled manually, as it is automatically disabled once the sub-interface is configured.
Also have in mind that the SPOKEs will be able to ping each other without additional configuration (remember that additional configuration IS required in the first to cases)
Three main concepts will be explained within this post:
- Frame Relay configuration on a Physical Interface + Inverse ARP
- Frame Relay configuration on a Point-to-Point Sub-interface
- Frame Relay configuration on a Multi-Point Sub-interface
DTE-DCE
There are two possible interface plugs in the Frame Relay cabling: DCE and DTE. I´m not going to go into details here, but what you do need to know as a Network Engineer are two things:
- If the interface is DCE you do need to provide the clocking on that side. Check the type using:
#show controller Serial0/0 | inc Clocks
and if you see "DTE V.35 Tx and Rx clocks detected" you are safe
If you want to FORCE the DCE and provide the clocking:
(config-if) #frame-relay intf-type dce
Inverse ARP
Like a regular ARP (Address Resolution Protocol) the Inverse-ARP is used to map the Layer 2 (DLCI in the case of Frame Relay) and the Layer 3 (IP Address).
When frame-relay is configured in a point-to-point manner there is no need to configure the mapping and the inverseARP is disabled by default.
When you configure the L2-L3 mapping manually, like in the Physical Interface configuration case (Case 1 of this post), you already have the mapping that the ARP provides, so you need to manually disable the inverse ARP.
1. Frame Relay configuration on a Physical Interface
When the Frame Relay configuration is done on a Physical interface, you need to do the following:
- Assign the IP to the interface
(config-if)#ip address 4.2.2.1 255.255.255.0
- Define the encapsulation using the Interface command:
(config-if)#encapsulation frame-relay
- Map the IP Address you want to access to the DLCI you have defined for that particular IP:
(config-if)#frame-relay map ip 4.2.2.2 201 broadcast
* Have in mind that DLCIs are only LOCALLY significant to the Router (DLCI value 201 will mean one thing to one router, and a totally different thing to another)
* "broadcast" is added because the local router will not be sending Broadcasts. The optional broadcast keyword in the frame-relay map command is required if broadcast and multicast traffic are to be sent over the specified dlci. Without the broadcast option, dynamic routing protocols such as EIGRP, OSPF and RIPv2 would not be able to advertise multicast route updates over the specified dlci.
Check the mappings using the following Privileged Mode command:
#show frame-relay map
Disable the inverse ARP (for reasons explained above)
(config-if)#no frame-relay inverse-arp
2. Frame Relay configuration on a Point-to-Point Sub-interface
For both of the following cases Frame-Relay encapsulation needs to be defined first on a Physical Interface bases, and the interface needs to be Administratively "UP". Create the Point to Point sub-interface and assign the IP address:
(config)#interface Serial0/0.12 point-to-point
(config-if)#ip address 4.2.2.1 255.255.255.0
Have in mind that there is no need to create the mapping L2-L3 because there is only one router on the other side of the PVC, so only one DLCI needs to be defined on the interface. For the same reason (L2-L3 mapping already defined) the inverse-ARP is disabled on this kind of sub-interfaces by default.
(config-if)#frame-relay interface-dlci 201
3. Frame Relay configuration on a Multi-Point Sub-interface
Create the Multipoint sub-interface and assign the IP address:
(config)#interface Serial0/0.123 multipoint
(config-if)#ip address 4.2.2.1 255.255.255.0
As there can be various routers on the other side of the PVC, the IP-DLCI mapping needs to be defined:
(config-if)#frame-relay map ip 4.2.2.2 102
(config-if)#frame-relay map ip 4.2.2.3 103
Unlike on the per-physical-interface basis, the inverse ARP doesn't need to be disabled manually, as it is automatically disabled once the sub-interface is configured.
Also have in mind that the SPOKEs will be able to ping each other without additional configuration (remember that additional configuration IS required in the first to cases)
CCIE: Preparation Schedule
So, you wanna be a CCIE?
It's true, I've read millions of how-to stories. Ok, maybe not millions, cause there are currently like 17k R&S CCIEs in the world, but... a lot!
Three of us made a detailed plan how to become CCIEs until January 25th 2014. If someone wants to join in in order to help each other and share the experience, let me know. There is already 3 of us in Madrid, Spain.
What you need to start
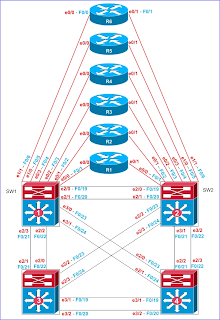
1. Topology like on the diagram. You can use:
- Actual Routers and Switches, preferably 3560s
- IOU (if you work in Cisco)
- Dynamips and connect it to Real Switches as explained here
2. Narbik Workbook 4.0 with all the Labs we're following. You can buy it from Micronics web page
3. CCIE Books
This is a pretty sensitive and confusing topic. If you look for what people recommend as the "must-read" to become a CCIE - you'll be disappointed because it's just so overwhelming, there is so much stuff! The thing is that I dont think people actually read all of those cover to cover, they just use them to consult small but specific issues.
I have a different approach, I have a few books that I own, highly recommend and I've read them many times cover-to-cover:
TCP/IP Illustrated, Volume 1: The Protocols (2nd Edition)
Routing TCP/IP, Volume II by Jeff Doyle (CCIE Professional Development)
Cisco QOS Exam Certification Guide (IP Telephony Self-Study) (2nd Edition)
CCIE Routing and Switching Certification Guide, 4th Edition by Wendell Odom, Rus Healy and Denise Donahue
and for the rest of the details I mostly use the RFC Recommendations. The problem with the CCIE is that the problems you will face are so specific that Google will not be able to help you... Sorry to disappoint you
CCIE Preparation Schedule, Part I: Narbik Workbook 4.0
Start Date: April 15th 2013
End Date: December 2nd 2013
Detailed Schedule:
It's true, I've read millions of how-to stories. Ok, maybe not millions, cause there are currently like 17k R&S CCIEs in the world, but... a lot!
Three of us made a detailed plan how to become CCIEs until January 25th 2014. If someone wants to join in in order to help each other and share the experience, let me know. There is already 3 of us in Madrid, Spain.
What you need to start
1. Topology like on the diagram. You can use:
- Actual Routers and Switches, preferably 3560s
- IOU (if you work in Cisco)
- Dynamips and connect it to Real Switches as explained here
2. Narbik Workbook 4.0 with all the Labs we're following. You can buy it from Micronics web page
3. CCIE Books
This is a pretty sensitive and confusing topic. If you look for what people recommend as the "must-read" to become a CCIE - you'll be disappointed because it's just so overwhelming, there is so much stuff! The thing is that I dont think people actually read all of those cover to cover, they just use them to consult small but specific issues.
I have a different approach, I have a few books that I own, highly recommend and I've read them many times cover-to-cover:
TCP/IP Illustrated, Volume 1: The Protocols (2nd Edition)
Routing TCP/IP, Volume II by Jeff Doyle (CCIE Professional Development)
Cisco QOS Exam Certification Guide (IP Telephony Self-Study) (2nd Edition)
CCIE Routing and Switching Certification Guide, 4th Edition by Wendell Odom, Rus Healy and Denise Donahue
and for the rest of the details I mostly use the RFC Recommendations. The problem with the CCIE is that the problems you will face are so specific that Google will not be able to help you... Sorry to disappoint you
CCIE Preparation Schedule, Part I: Narbik Workbook 4.0
Start Date: April 15th 2013
End Date: December 2nd 2013
Detailed Schedule:
Narbik in web-iou
Narbik Topology for web-iou
Disclaimer:
I DON’T OWN NOR HAVE AN ACCESS TO THE TOPOLOGY, INITIAL CONFIGS, IOU/IOL BINARIES OR ANY OTHER MATERIAL UNDER CCIE EXAM, NARBIK OR COPYRIGHTED FROM CISCO OR ANY OTHER VENDOR.
This tutorial is for those who:
- Are Cisco (or Cisco Partner) Employees, and therefore have an access to the Cisco IOU tool
- Have purchased Narbiks Workbook 4.0 in order to prepare for the CCIE exam
Ok, now that I´m "safe", lets get into the real deal
I used the awesome tool called "web-iou" made by Andrea, and published on his RouterReflector page, where you can find instructions on what it´s for and how to use it:
http://www.routereflector.com/it/cisco/cisco-iou-web-interface/
P.S. Congrats to Andrea for recently becoming a CCIE!!!
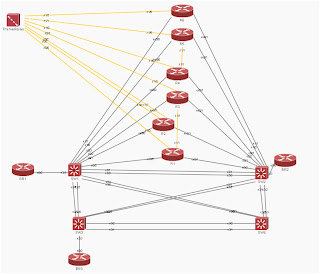
By this point I suppose that you´re familiar with Narbik´s method of teaching CCIE, and the basic L2 Ethernet and L3 topologies that his WorkBooks are based on.
Step 1: DOWNLOAD the topology. Do not unzip the file!!!
http://www.4shared.com/archive/-kkyMIa1/iou-narbik-mat.html
Step 2: IMPORT the Topology into the web-iou
Manage -> Import Labs and locate the downloaded .gz file
Step 3: Go to Laboratories and enter the Narbik_by_Mat Lab
You will see the following topology under the "Diagram" tab:
You will probably immediately notice the similarity with the Narbiks Topology. The only difference are the interfaces. I tried re-programming it in the NETMAP, but without success. So far the IOU offers only simple Ethernet interfaces, and only 4-interface Line Cards (makes it impossible to get the Fa0/19 interface for example).
The temporal solution I´m using is the Diagram you will find under the "Narbik_IOU_by_Mat" tab. It´s a simple diagram that has my topology interfaces marked in RED color, and the original Narbik ones marked in BLUE. You can do the Narbik Labs using my topology, and have this Diagram in front of you for convenience only.
Enjoy the experience, and let me know if you have any ideas how I could improve it!
Subscribe to:
Comments (Atom)
Most Popular Posts
-
Before we start, lets once again make sure we fully understand what Bridge Domain is. The bridge domain can be compared to a giant distribut...
-
Ever since Cisco bought Insieme and created Cisco ACI, and VMware bought Nicira and created NSX, I've been intensively deep-diving and b...
-
Before I get into the Python for NX-OS, let me explain a few concepts that I've seen Network Engineers have been struggling with. Dev...
-
By know you should know the following facts about ACI: Cisco Nexus 9k Switches make the ACI Fabric, which is the Control and the Data pla...
-
The VM-Series firewall for VMware NSX is jointly developed by Palo Alto Networks and VMware. NetX APIs are used to integrate the Palo Alto N...
-
[In collaboration with the guest blogger, Marc Espinosa ] Let's start with the messaging protocols, MQTT and CoAP, and consider which ...
-
Google has made their Cloud Platform (GCP) so that you can host your application any way your business requires. When we talk about the ...
-
First time we “unpack” ACI, we will find a certain number of potential Spine and potential Leaf switches, and hopefully 3 (or 5) APIC Contro...
-
Before we get deeper into the ACI (Application Centric Infrastructure) as the Cisco's official SDN solution, we need to clarify a few te...
-
First be sure which type of LSA you need to filter by making sure in which part of database the route is: #show ip ospf database [router ...